Apple Issues a Rare Security Warning:
Why iPhone Updates Matter More Than Ever
In March 2026, Apple confirmed that security researchers identified active web‑based attacks targeting iPhones running outdated versions of iOS.
In March 2026, Apple confirmed that security researchers identified active web‑based attacks targeting iPhones running outdated versions of iOS.

Apple does not frequently issue public security warnings, which is why this one deserves attention. In some cases, simply visiting a compromised website or clicking a malicious link was enough to put data at risk.
For businesses, this matters more than it may seem at first glance. Employee iPhones are commonly used to access Microsoft 365 email, files, Teams, and authentication prompts. When those devices fall behind on updates, they quietly become one of the easiest ways attackers can bypass stronger perimeter defenses.
Industry data supports this concern. According to Verizon’s 2024 Data Breach Investigations Report, over 70 percent of breaches involved exploitation of known vulnerabilities where a patch was already available. In other words, many incidents are preventable with basic update hygiene.
Apple’s advisory explains that the attacks specifically target out‑of‑date versions of iOS through malicious web content, not risky apps or unusual behavior. A user does not have to do anything obviously unsafe for the vulnerability to be triggered. [support.apple.com]
Key points from Apple’s guidance:
This public warning is unusual for Apple and signals that these attacks are being observed in real‑world conditions, not just in labs.

From an IT strategy perspective, this alert highlights a pattern we see regularly with small and mid‑sized businesses. Mobile devices are often treated as personal tools rather than business endpoints.

The reality is that most phones contain:
Once compromised, a phone can be used to move laterally without triggering traditional security alerts.
This aligns with broader industry trends. IBM’s Cost of a Data Breach Report shows that organizations with unmanaged or partially managed endpoints experience higher breach costs and longer containment times. Mobile devices are frequently part of that blind spot.
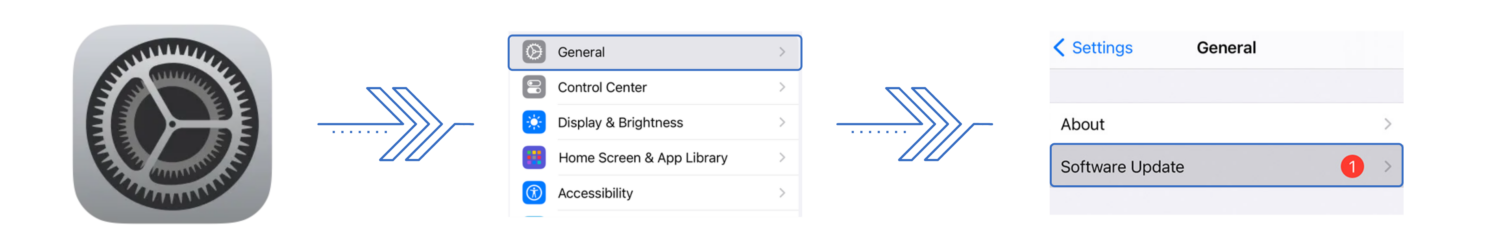
Updating an iPhone is one of the simplest and most effective security steps a user can take.
Recommended steps
For older iPhones that cannot support the newest iOS version, Apple still recommends installing the latest security update available for that device model.
According to Apple, devices that remained fully updated were not at risk from the reported attacks.
While updates are critical, this warning also reinforces the importance of having a broader mobile and identity strategy.
A few practical steps businesses should consider:
Security incidents rarely come from a single failure. They usually result from small gaps that accumulate over time.
Security warnings make headlines, but real protection comes from the habits and systems behind the scenes. Device updates, access controls, and visibility into how company data is accessed are all foundational parts of a proactive IT strategy.
At SBT Partners, we help businesses think through these details, so security doesn’t rely on luck or last‑minute fixes. When devices, users, and policies are aligned, risk naturally decreases.
If you want help reviewing how employee devices fit into your broader IT plan, our team is here to guide you. Get a free IT health check to see where you may be exposed by filling out the form at this link.








This site uses cookies. By continuing to browse the site, you are agreeing to our use of cookies.
AcceptLearn moreWe may request cookies to be set on your device. We use cookies to let us know when you visit our websites, how you interact with us, to enrich your user experience, and to customize your relationship with our website.
Click on the different category headings to find out more. You can also change some of your preferences. Note that blocking some types of cookies may impact your experience on our websites and the services we are able to offer.
These cookies are strictly necessary to provide you with services available through our website and to use some of its features.
Because these cookies are strictly necessary to deliver the website, refusing them will have impact how our site functions. You always can block or delete cookies by changing your browser settings and force blocking all cookies on this website. But this will always prompt you to accept/refuse cookies when revisiting our site.
We fully respect if you want to refuse cookies but to avoid asking you again and again kindly allow us to store a cookie for that. You are free to opt out any time or opt in for other cookies to get a better experience. If you refuse cookies we will remove all set cookies in our domain.
We provide you with a list of stored cookies on your computer in our domain so you can check what we stored. Due to security reasons we are not able to show or modify cookies from other domains. You can check these in your browser security settings.
We also use different external services like Google Webfonts, Google Maps, and external Video providers. Since these providers may collect personal data like your IP address we allow you to block them here. Please be aware that this might heavily reduce the functionality and appearance of our site. Changes will take effect once you reload the page.
Google Webfont Settings:
Google Map Settings:
Google reCaptcha Settings:
Vimeo and Youtube video embeds:
